The hidden web beckons with its allure of anonymity and forbidden territory. For those brave enough to explore, the layered networks known as Onionlinks offer a glimpse into a world beyond the surface web's grasp. But navigating this labyrinth requires a keen mind and onionlinks a courage to decode its enigmas.
- The first step is understanding the design of the Onionlink, where layers of encryption mask your identity and data from prying eyes.
- Advanced software tools are required to enter these hidden networks, reformatting ordinary data into an unreadable jumble.
- Within the depths of the Onionlink, you may find a vast array of content, from underground forums to classified files.
However, tread carefully. The untamed nature of the deep web shelters both malicious actors, making it a risky environment for the unwary.
Exploring the Labyrinth: A Guide to Onionlinks
Onionlinks, also known as hidden links, are like secret passages on the internet. They lead you to alternative corners of the web, often hidden behind layers of encryption and anonymity. To explore these labyrinthine paths, you'll need a steady hand and an open mind. First, remember that onionlinks are often found on rare platforms or sites. Don't expect them to be listed in your usual search results.
- Secondly , you'll need a compatible application like Tor, which allows you to browse anonymously and securely.
- Always aware that the content behind onionlinks can be unverified. Exercise caution and critical thinking when exploring these uncharted territories.
Onionlinks offer a unique opportunity to discover hidden aspects of the internet. They can lead you to underground communities, censored information, or even artistic expressions that wouldn't be found elsewhere. But remember, with great access comes great responsibility. Always maintain your online security.
Tor Link Anonymity: Surfing the Hidden Web Safely
Venturing into the dark web requires a commitment to protection. While Onionlink offers a layer of anonymity, it's crucial to utilize additional strategies to reduce threats. A reputable encryption tool can further protect your connection, while utilizing sound digital hygiene habits is indispensable.
- Remember that the hidden web can be a volatile space, and exercise vigilance when engagingwith users.
- Avoid sharing sensitive information unless you have verified the recipient.
- Keep up-to-date to patch any weaknesses that could be targeted by malicious actors.
By understanding the inherent perils and taking steps, you can surf the hidden web more safely.
Venture Into the World of Onionlinks
The realm of hidden connections can be a mysterious place. It's a world beyond the surface, overflowing with secrets just waiting to be uncovered. Navigating these obscure routes can be tricky, but for those curious enough, the rewards might be incredible.
- Get Ready yourself for a surprising adventure.
- Dive into the mysterious landscapes of the onionlinks world.
Proceed with caution though, as this virtual wilderness is not for the faint of heart. It's a place where lines are crossed, and you never know whatyou might find.
Hidden Treasures: Finding Value in the Onionlink Network
The decentralized nature of the Onionlink network often leads to overlooked treasures. While many concentrate their attention on more established platforms, savvy users are unearthing hidden worth within this unique ecosystem.
- From niche communities to groundbreaking projects, Onionlink offers a platform for individuals to connect in ways not possible elsewhere.
- By exploring into this often overlooked network, users can tap into a wealth of insights and potentially benefit.
Whether you're a seasoned blockchain enthusiast or simply curious about the future of the internet, Onionlink presents an compelling opportunity to participate in something truly revolutionary.
Delving into the Shadows of Onions: Hazards and Vulnerabilities of Onion Connections
While hidden internet hubs can offer a degree of anonymity and access to otherwise unavailable information, they also harbor a host of dangers. Users venturing into these shadowy realms run the risk of encountering online predators, who may attempt to exploit vulnerabilities. Illegal activities are rife on onion networks, making it a breeding ground for illegal transactions. Additionally, the inherent anonymity can embolden users to engage in cyberbullying, with little fear of consequences.
- Be cautious when accessing information on onion networks..
- Implement comprehensive security protocols, including a VPN and complex passwords..
- Be aware of the potential risks and avoid sharing sensitive information..
 Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now!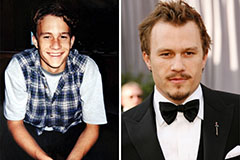 Heath Ledger Then & Now!
Heath Ledger Then & Now! Elisabeth Shue Then & Now!
Elisabeth Shue Then & Now!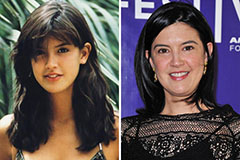 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Nicki Minaj Then & Now!
Nicki Minaj Then & Now!